Take Our Quiz on Multi-factor Authentication (MFA)

Over 80 percent of hacking-related breaches are caused by stolen or weak passwords:
True. Hackers use nefarious methods like keylogging, pharming, and phishing to get access to usernames and passwords. Verizon's Data Breach Investigations Report shows 81% of hacking-related breaches leveraged either stolen and/or weak passwords. MFA is a simple, inexpensive security measure that adds additional authentication factors that hackers are not likely able to intercept.
MFA prevents more than 99.9% of account compromises:
True. MFA primarily prevents any attack that results from a bad actor obtaining or guessing the user’s credentials. This can include a wide range of cyberattacks, though most commonly this encompasses phishing/spear-phishing attacks, automated credential stuffing, and guessing attacks. Microsoft’s analysis has determined that 99.9% of account compromises can be blocked with MFA.
What are the types of authentication methods used in MFA?
A, B, and C. MFA adds an extra layer of security by requiring two or more verification factors during the login process. You start with something only you know (username and password), then you must enter another factor such as a one-time, system-generated password or token that is sent to your phone or a biometric identifier like a fingerprint or voice recognition. Other authentication systems may require users to log in to a VPN with a valid certificate to access the network.
One-time password (OTP) tokens were originally hardware devices but can now be software and have become one of the most common MFA factors. Which of the following statements are true:

All of the above. One of the most common MFA factors is a one-time password (OTP) which is a 4-8 digit code received via email, SMS, or mobile app. The code is generated periodically or each time an authentication request is submitted and is based upon a seed value that is assigned to the user when they first register or another factor such as a counter that is incremented or a time value.
Two-Factor Authentication (2FA) is a subset of MFA:

True. MFA is often used interchangeably with two-factor authentication (2FA). 2FA always requires two factors to verify the user’s identity while MFA could involve two or more factors. Multi-factor simply means any number of factors greater than one.
MFA is only beneficial for companies of a certain size:

False. Any company, regardless of size, should adopt an MFA solution as part of its security strategy. The data small and medium-sized businesses (SMBs) want to protect is no less sensitive and the disruption is no less serious. MFA is typically not complex, costly, or frustrating.
What should you do if you receive a security code when you are not trying to log in to your account?

Contact your IT Manager to confirm authenticity. If you receive a security code or push notification when you’re not trying to log in to your account, it may be that someone else is attempting to do so. It could also be a cached token as a result of Outlook, Teams, etc. needing to be refreshed. If this happens, contact your IT department or manager to evaluate the cause and change your password if necessary.
I don't have anything confidential in my account, so I don’t need to worry about multi-factor authentication:
False. Most attackers aren't interested in your personal account but using your username and password to break into the secure internal network to look for vulnerabilities on the sensitive internal systems connected to that network. Alternatively, attackers will log in to a user’s email account and send out phishing messages to other employees in an attempt to compromise their computers and get access to sensitive information.
The use of personal devices is not a strict requirement for MFA:
True. Instead of personal devices, administrators may opt for hardware tokens or non-mobile device software token generators. However, if your organization decides to require a personal device for MFA, then you should add MFA to your Bring Your Own Device (BYOD) policy to send a clear signal to users on the acceptance of their personal devices for MFA purposes.
You should set up MFA on all applications you access through the internet or a VPN:
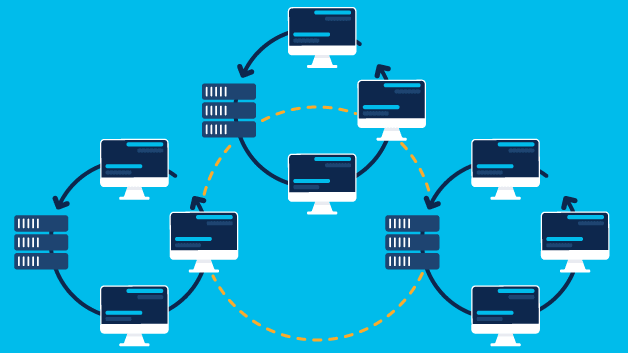
True. Any business application accessed through the public internet will present some risk, whether to customer data or business continuity, if an account is compromised. To offset the amount of work it would take to secure multiple identities, companies shouldn't reduce MFA but reduce the number of identities users have. Consolidate identities by using a single source (or two) and then use SAML authentication single sign-on (SSO) wherever possible.
You got {number correct} / 11 answers correct.

You got {number correct} / 11 answers correct.